Key Takeaways:
- Paolo D’Amico says AI agents will shift identity management to a central role over the next 5 years.
- Integration of Agentkit and x402 secures transactions for 1 verified person per authorized agent.
- By 2026, World ID uses ZK cryptography to stop bots by requiring proof that you are a new person.
The Death of the ‘Repetitive Bot’
For years, the battle against Sybil attacks—where a single actor creates a multitude of fake identities to subvert a system—was a game of detecting bot-like behavior. If a thousand accounts moved in perfect synchronization or used the same rigid script, security systems could easily flag them as malicious.
However, the integration of artificial intelligence (AI) is fundamentally dismantling these traditional defenses. In an interview with Bitcoin.com News focused on the evolving threat landscape, Paolo D’Amico, senior staff product engineer at Tools for Humanity, outlined how AI has transitioned from a technical tool to a sophisticated “force multiplier” for digital attackers.
In the past, executing a Sybil attack at scale required significant technical overhead to ensure the “clones” appeared distinct. According to D’Amico, AI has lowered this barrier to entry by automating the creation of credible personas.
“AI makes that automation both easier to deploy and more convincing in practice,” D’Amico notes. “It expands an attacker’s ability to generate realistic behavior, adapt dynamically, and bypass existing security controls.”
Unlike traditional bots that follow static code, AI-driven agents can generate unique social media posts, engage in varied onchain transactions, and mimic the “jitter” of human timing. This dynamic adaptation makes it nearly impossible for legacy security systems to identify a cluster of accounts as being controlled by a single entity.
Perhaps the most significant shift D’Amico identifies is a fundamental change in how we perceive automated traffic. Historically, security teams operated under a simple criterion: Automated traffic is bad; human traffic is good. Yet, as we move toward an era of decentralized AI agents that perform legitimate tasks, that binary is breaking down.
“Agents are providing a new interface for interacting online, which makes it harder to distinguish harmful automation from legitimate or desired automated activity,” D’Amico explains. “As a result, sites now need to adapt their defenses for a world where automation itself is no longer a reliable signal of abuse.”
Is CAPTCHA Dead?
If AI can solve puzzles and mimic human browsing patterns, the question arises: Is the traditional CAPTCHA dead? According to D’Amico, these tools are not necessarily disappearing, but they are undergoing a radical evolution.
Relying on simple puzzles is becoming a game that AI is increasingly winning. Instead, robust solutions must move toward fundamentally representing a human better in the digital world. D’Amico points to emerging standards like those from the Privacy Pass working group as a glimpse into a future where “human-in-the-loop” actions are verified through deeper technological layers.
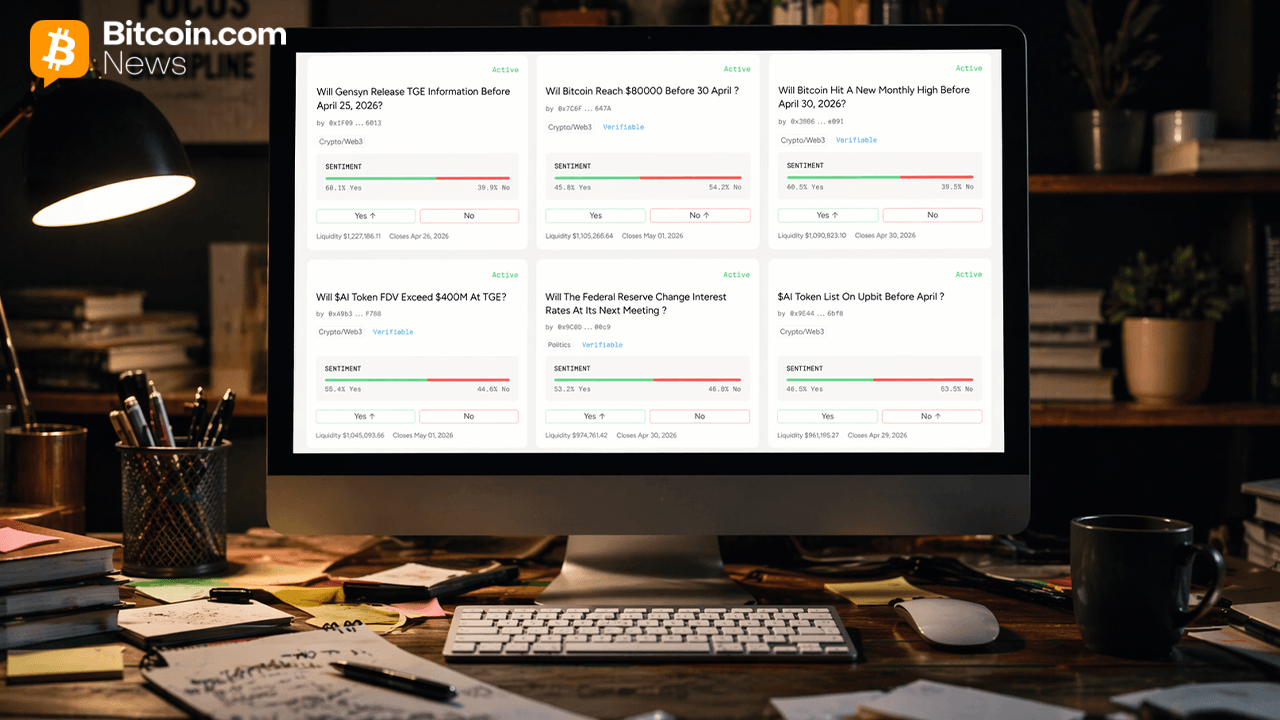
To combat the threat of a Sybil swarm of autonomous agents, new infrastructure is emerging that prioritizes verified uniqueness. One such solution is Agentkit, an SDK based on the World ID Protocol.
By integrating Agentkit, websites can gate, limit, or control access to content based on rules set for World ID credentials. The most immediate application is rate limiting based on unique humans. For instance, a platform could allow each verified person a set number of requests within a specific timeframe, effectively neutralizing the advantage of mass-produced bot accounts.
According to D’Amico, World ID introduces a security layer where scaling Sybil attacks becomes significantly more difficult. In this ecosystem, an attacker can no longer gain a new identity simply by providing a new email address or phone number. To the system, you must be a new person. This shift is anchored by the Orb—a sophisticated piece of trusted hardware—and the use of zero-knowledge (ZK) cryptography, ensuring uniqueness is verified without compromising individual privacy.
As the economy of autonomous agents grows, the challenge moves from mere identification to authorization. New protocols like x402 enable agents to pay for web resources directly. However, the critical security question remains: How do we know an agent is spending on behalf of a human rather than acting as a rogue script?
The Regulatory Horizon: Privacy as a Foundation
D’Amico explains that the integration of x402 and Agentkit provides a “power of attorney” model for the digital age. While x402 handles the payment mechanism, Agentkit verifies the authority behind the request.
“Through AgentKit, a user can delegate presenting their proof of human to an agent,” D’Amico says. “In that model, a World ID can have multiple authorized keys that are allowed to generate proofs. One key belongs to the user’s device, and the user can also authorize an agent key through AgentKit.”
This means that when an agent makes a payment via x402, it carries a cryptographic signature proving it was explicitly authorized by a verified human. Crucially, this authority is limited: The agent can act within its granted permissions, but it cannot alter the user’s World ID or seize control of the identity more broadly.
As these technologies push the boundaries of digital identity, they do not exist in a vacuum. The path forward for innovation is closely tied to the shifting sands of global regulation. D’Amico views the evolution of regulatory frameworks not as a hindrance, but as an essential companion to technological growth.
“As AI continues to advance, we expect regulatory frameworks around identity and privacy to evolve in conjunction with the technology,” D’Amico observes. “These advances will reshape the landscape, opening new opportunities while also introducing new risks and attack vectors.”
Looking toward the next five years, D’Amico projects that identity management will shift from a peripheral security feature to a central pillar of the internet. In an “AI-native” world, the definition of identity must expand to cover both the creator and the emissary.
“For humans, that means stronger verifiable trust anchors that allow identity to remain a reliable representation of a real person online,” D’Amico predicts. “In parallel, I expect identity frameworks for autonomous agents to become more important.”
As agents begin to interact with financial systems and platforms in more meaningful ways, the industry will require clearer ways to verify who or what they represent, the extent of their authority, and whether they are acting on behalf of a real user.